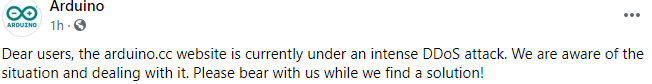
This isn’t a hacking tutorial but we will take a look at the anatomy of a DOS and DDOS attack to get an idea of how a small IOT device like an Arduino with an Ethernet Shield can be used to cause a server to do massive amounts of work.
Security
LensLok – Early 80’s Anti-Piracy that frustrated | MVG
In 1985, in an effort to combat software piracy. ASAP Developments invented the LensLok – a plastic lens in a foldaway frame.The LensLok device was essentially a row of prisms arranged vertically in a plastic holder. In this video we take a closer look at the LensLok to understand how it works, and why it ultimately failed as an anti-piracy device.
How a Laser-Shot Disk Defeats Hackers & Pirates
Shooting Holes in Disks with a Laser is Incredible when it comes to Retro Copy Protection. Find out how in this episode of Coding Secrets.
Spying Robot Vacuums Really Suck
LidarPhone exploits the LiDAR sensor in robotic vacuums to eavesdrop on your private conversations.
Just when you thought you had all your bases covered for privacy, it turns out that even your seemingly innocent robot vacuum may be spying on you. And all this time you thought it was only collecting dirt from the floor.
A team in Singapore took advantage of the LiDAR sensor typically found onboard robotic vacuums for navigation purposes, and repurposed it to capture sound with an exploit that they call LidarPhone. Laser microphones, in which laser beams reflected off of vibrating objects are converted into audio, are not a new idea. However, laser microphones require sophisticated setups and fine-tuning that is not possible with a stock vacuum cleaner. Getting a vacuum to work as a laser microphone took some clever thinking.
SSH Honeypot in 4 Minutes – Trap Hackers in Your Server
In this video I’ll show you a funny way to protect your SSH server from hackers, script kiddies and Chinese botnets, using Endlessh by Chris Wellons Endlessh (GitHub): https://github.com/skeeto/endlessh
Pwnagotchi – Pwn all the wifi
Pwnagotchi is a modern day take on the Tamagatchi of the 90s, but with a Cyber Security twist. This digital pet derives his happiness by sniffing WPA and WPA2 handshakes which can then be run through hashcat to guess the password. Two or more Pwnagotchis in range of each other will communicate and split the workload. The Pwnagotchi can also send its stats back to the internet to rank your Pwnagotchi against other Pwnagotchis from around the world.
Secrets of the Nintendo Game Boy Boot Logo | MVG
The Nintendo Game Boy has a clever form of Anti Tamper that made it difficult for unofficial and bootleg games to be developed for it and it was all thanks to the Nintendo Logo thats displayed when you power on the handheld. Lets take a closer look at the Boot process of the Game Boy.
This Black Box Reads RFID Cards in Your Pocket
This Black Box Reads RFID Cards in Your Pocket
How to fine-tune pfSense 2.4.5 for 1Gbit throughput on APU2/APU3/APU4
Background information
APU2, APU3 and APU4 have four 1Ghz CPU cores, pfSense by default uses only 1 core per connection. This limitation still exists, however, a single-core performance has considerably improved. With new BIOS, and settings described below, pfSense can route about 750-800Mbit/s on one connection.
APU2*4 have very performant Intel I210-AT Network Interfaces. These NICs have 4 transmit and four receive queues, being able to work simultaneously on 4 connections. With some fine0tuning, pfSense can take advantage of this and route at 1Gbit when using more than one connection.